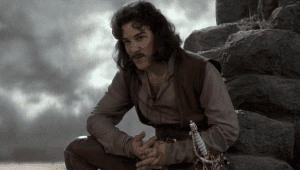
I do not think that word means what you think it means…
“I do not think that word means what you think it means”
– Inigo Montoya, The Princess Bride
As with any other scientific specialty, computer investigations have their own lexicon of ideas and terms. Many of them are foreign enough that a layman will require an explanation just to understand them, but several are words with which most people will be familiar that have a distinct meaning in the context of forensic examination of electronic evidence. Some of these are outlined below.
Image
Both the standard idea – “a picture” and the forensic meaning are used. The forensic term “image” refers to a forensically sound capture of evidence into a file format that allows for examination. It is an exact duplicate of the original device’s data, in a new format. “Bob took an image of the hard drive and then photographed an image of the computer from which it came.”
Acquire
Typically not used by experts in the traditional meaning “to obtain” but rather in the forensic sense “to obtain an image of (see above)” – when an expert says that they “acquired the hard drive” they normally mean that they made a forensic image of it, not that they got their hands on it.
Hash
Not the fried potatoes you have for breakfast, but a mathematical formula used to represent the unique fingerprint of a file. “I compared the hashes of the two files and determined they were identical.”
Accessed
This is a particularly troublesome term. In computer forensics, this indicates that the computer has ‘touched’ the file in some way, whether by a user or by the computer’s own internal programs. Files are often “accessed” by things like virus scanners that occur without the user’s knowledge. This is in distinct contrast to the layman’s concept of “accessed” on a computer – meaning a user interacted with a file, by opening it, for example.
Viewed
Like accessed, this term can be confusing and is often the source of misunderstanding by non-experts. If an expert says that a web page is “viewed” they mean that it was loaded in a browser. It does not necessarily indicate that human eyes saw the whole page – or indeed that any of it was actually seen. Forensic analysis can sometimes give strong indications that a page was actually seen by human eyes – perhaps by showing that information on a page was followed by a web search of that information, or that a link in a page was clicked on – but ultimately, there is no incontrovertible evidence that a human being has “viewed” a web page on the computer.
Deleted
When we think about the phrase “deleted files” most of us think of this as an intentional action. We imagine a user selecting some files and dragging them to the Recycle Bin or hitting their Delete key. In actuality, deleted information can often be deleted by the normal operation of the computer, as is the case with Temporary Internet Files. It is therefore important that the understanding of the term “deleted” and its usage in a particular situation be well-defined.
As you can see from these few examples, when using precise terms-of-art in a legal setting, it is crucial that the speaker and the listener both be understanding the term in the same way. Ensuring this is the case is one of the keys to a successful computer forensic examination.